Новости о Attack Well [ Фото новости ] [ Свежие новости ] | |
Absurdistan: For $2.5k per day, you can attack Verge (XVG). For $44k you can shut down Electroneum (ETN) as well.
A 51% attack means that 51% of the ‘computer processing power’ used to verify transactions is controlled by one entity, and once this number (51%) has been reached, they can create a new ledger (blockchain ‘fork’ basically) so that they can double spend their own coins (among a few other capabilities). дальше »
2019-3-1 01:51 | |
|
|
Grim Stories of Ethical, Privacy Abuses Emerge About Coinbase’s New Partners
When Coinbase acquired Neutrino for an unspecified amount in February 2019, the news looked like business as usual: A cryptocurrency juggernaut had made another acquisition. дальше »
2019-3-1 17:19 | |
|
|
Op Ed: Why It’s Unsafe to Store Private Crypto Keys in the Cloud
There are two primary reasons why storing your private crypto keys in the cloud is a bad idea. First, your cloud provider represents a centralized honeypot that could experience a security breach, allowing cyber criminals to access your data. дальше »
2019-2-19 00:19 | |
|
|
New Zealand Police Report States Cryptopia Hack Investigation Has Been Progressing Well
The police force from New Zealand has recently emitted a report stating that it has been making important progress on the case of the local crypto exchange Cryptopia, which was hacked and lost over $16. дальше »
2019-2-7 22:53 | |
|
|
The Proof-of-Stake Pandora’s Box—A “Rich Get Richer” Formula?
It has been six days since Constantinople had to be forcefully put off because of a bug. Chain Security sniffed out the vulnerability just before miners upgraded gifting hackers—who appear to be on the prowl, to not only siphon out hard earned funds but revive the memories of 2016 DAO attack that as well all […] The post The Proof-of-Stake Pandora’s Box—A “Rich Get Richer” Formula? appeared first on Ethereum World News. дальше »
2019-1-22 15:30 | |
|
|
BetterHash Protocol Lets Pool Miners Regain Control Over Their Hash Power
One problem that concerns many is the centralization of mining within the Bitcoin ecosystem. Fortunately, there are talented developers working to solve this problem and Matt Corallo, full-time Bitcoin developer at Chaincode Labs, is one of them. дальше »
2019-1-26 23:50 | |
|
|
Wyoming’s New Bill Seeks to Bring Order into the World of Crypto
The world of cryptocurrencies faces many challenges. They include price volatility as well as low mainstream uptake. Cryptos are also susceptible to a 51 percent attack as was seen recently with Ethereum Classic. дальше »
2019-1-19 13:43 | |
|
|
Ten Years Later, a Reflection on Bitcoin’s Genesis and Satoshi’s Timing
October 31, 2008, and January 3, 2009. The two dates have cemented themselves with Promethean significance into Bitcoin’s lore. On the October 31, Satoshi Nakamoto published the Bitcoin white paper, a constitution of sorts for his revolutionary monetary system and its intrinsic currency. дальше »
2019-1-3 07:14 | |
|
|
Security Researchers Reveal Wallet Vulnerabilities On Stage at 35C3
In a demonstration titled “Wallet. fail,” a team of security researchers hacked into the Trezor One, Ledger Blue and Ledger Nano S. Unfortunately, it appears as if their findings were first put on display at the 35th Chaos Communication Congress (35C3) in Leipzig, Germany, rather than through accepted Responsible Disclosure practices, which would have allowed the manufacturers to patch the vulnerabilities and protect their customers from any potential attack. дальше »
2019-1-1 19:15 | |
|
|
One Day After the Bitcoin Cash Hard Fork: Takeaways and Latest Developments
Bitcoin Cash, the “big block” project that forked away from the Bitcoin blockchain in August 2017, “hard forked” (split) into two different coins: “Bitcoin Cash ABC” (BCH ABC) and “Bitcoin Cash SV” (BCH SV). дальше »
2018-11-17 02:13 | |
|
|
Report: Cryptocurrency Mining Attacks Likely to Surge in the Future
Kaspersky Lab’s cyber threat and research arm Securelist published a report on November 13, 2018, which provides details on the rising trend of cyber attacks on cryptocurrency exchanges in Q3 2018. The report also mentions prominent cyber attack groups including Lazarus as well as observing massive growth in crypto mining attacks. дальше »
2018-11-15 10:00 | |
|
|
Researchers Link NotPetya Outbreak and Kiev Power Grid Outage to one Hacking Group
Depending on how one looks at the world, coincidence is either a common thing or doesn’t exist at all. In the world of cyberthreats, it would seem the latter is the more common conclusion. New research shows the NotPetya ransomware attack, as well as a disruption of Ukraine’s power grid, are linked together by one […] The post Researchers Link NotPetya Outbreak and Kiev Power Grid Outage to one Hacking Group appeared first on NullTX. дальше »
2018-11-8 18:58 | |
|
|
OmiseGO Presents an ‘Achievable Roadmap’ to Survive Bear Market
OmiseGo, one of the more promising token, published a roadmap detailing its future map in the coming months on Medium on October 30, 2018. Learning from previous experiences, the blog post stated that instead of revealing plans well in advance, they decided to list their achievements to-date to avoid disappointments. дальше »
2018-11-2 10:00 | |
|
|
TRON Still Best Performer Against BTC, XRP & ETH
In recent months, TRON has seen some slight upward movement and currently sits at number eleven on the top 100 cryptocurrencies on CoinMarketCap. September is where TRON really found its legs as it was listed on the Crypto Exchange Platform. дальше »
2018-10-10 13:30 | |
|
|
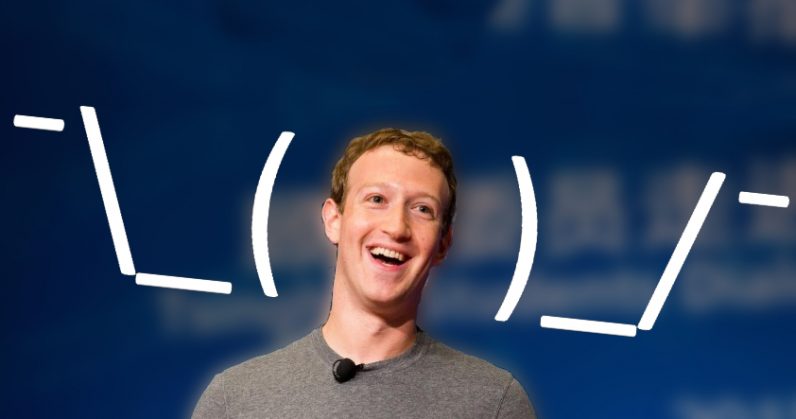
The free internet makes us the product — we need to stop it
The bad headlines continue to stack up for Facebook this year: from the Cambridge Analytica scandal, to the New York Times report that Facebook gave Apple, Samsung, and other mobile device makers access to its users personal data without permission, to the revelation that the firm routinely gives user information and preferences to several Chinese telecommunications firms, to last week’s security breach in which hackers took control of 50 million user accounts as well as any third-party sites those users logged into via Facebook. дальше »
2018-10-6 19:30 | |
|
|
What Bitcoin Did Gets Technical with Crypto-Educator Jimmy Song
<iframe style="border: none" src="//html5-player. libsyn. com/embed/episode/id/7132345/height/90/theme/custom/autoplay/no/autonext/no/thumbnail/yes/preload/no/no_addthis/no/direction/backward/render-playlist/no/custom-color/87A93A/" height="90" width="100%" scrolling="no" allowfullscreen webkitallowfullscreen mozallowfullscreen oallowfullscreen msallowfullscreen></iframe> On the latest episode of What Bitcoin Did, host Peter McCormack interviews Jimmy Song, a consultant in blockchain education, to take an in-depth look at a relatively recent incident in the world of cryptocurrency and use that as an example to segue into a deeper discussion on the possible trajectories of Bitcoin itself. дальше »
2018-10-6 00:05 | |
|
|
McAfee Report: Cryptocurrency Mining Malware to only Grow in Magnitude
The crypto community is well aware of cryptojacking – a crypto-malware attack that uses the hosts’ computer power to mine cryptocurrencies without their knowledge. In what comes as unfortunate news for the budding community, the problem is only going to get worse. дальше »
2018-9-27 23:00 | |
|
|
Study Reveals Growing Sophistication in Malicious Mining of Cryptocurrency
Several Chinese researchers from Fudan University, Tsinghua University and the University of California Riverside have produced the first systematic study of the malicious mining of cryptocurrencies, known as cryptojacking, unveiling increasing complexity over time. дальше »
2018-9-25 23:59 | |
|
|
Bitcoin Gold (BTG) Gets Delisted By Bittrex Crypto Exchange Due To $18 Million Hack
Bittrex Exchange Removes Bitcoin Gold From Their Exchange Among cryptocurrency startup companies, the risk of theft, extortion, or major attack is very significant. The cryptocurrency community has always been especially susceptible to crime, because of the prevalence of technology-minded hackers in the markets, as well as the anonymous nature of cryptocurrencies in general. For these […] дальше »
2018-9-4 13:37 | |
|
|
A Guide to 99% Fault Tolerant Consensus
Special thanks to Emin Gun Sirer for review We’ve heard for a long time that it’s possible to achieve consensus with 50% fault tolerance in a synchronous network where messages broadcasted by any honest node are guaranteed to be received by all other honest nodes within some known time period (if an attacker has more than 50%, they can perform a “51% attack”, and there’s an analogue of this for any algorithm of this type). дальше »
2018-8-9 04:03 | |
|
|
Bitcoin Magazine’s Week in Review: Challenging the Way It’s Always Been Done
This past week, we talked to three security experts about how to design smarter and more secure smart contracts. Google is dipping its toe in the blockchain waters by introducing integrations for applications built with Ethereum and Hyperledger. дальше »
2018-8-5 16:08 | |
|
|
Audits and Quality Assurance: Patching the Holes in Smart Contract Security
On July 10, 2018, news broke that cryptocurrency wallet and decentralized exchange Bancor was hit with a hack. A wallet the Bancor team used to update the protocol’s smart contracts was infiltrated, and the $23. дальше »
2018-8-3 19:24 | |
|
|
Are you afraid of cyber attacks? Improve your cyber security!
Even though we are well into our second decade of widespread internet use, the term ‘cyber attack’ is still a relatively new and daunting one for many people. Many individuals and small businesses entrust their cybersecurity to off-the-shelf antivirus softwares, which can effective but certainly aren’t foolproof. When it comes to preventing cyber attacks, everyone […] дальше »
2018-7-27 16:04 | |
|
|
Governance, Part 2: Plutocracy Is Still Bad
Coin holder voting, both for governance of technical features, and for more extensive use cases like deciding who runs validator nodes and who receives money from development bounty funds, is unfortunately continuing to be popular, and so it seems worthwhile for me to write another post explaining why I (and Vlad Zamfir and others) do not consider it wise for Ethereum (or really, any base-layer blockchain) to start adopting these kinds of mechanisms in a tightly coupled form in any significant way. дальше »
2018-7-21 23:03 | |
|
|
STARKs, Part I: Proofs with Polynomials
Special thanks to Eli Ben-Sasson for ongoing help, explanations and review, coming up with some of the examples used in this post, and most crucially of all inventing a lot of this stuff; thanks to Hsiao-wei Wang for reviewing Hopefully many people by now have heard of ZK-SNARKs, the general-purpose succinct zero knowledge proof technology that can be used for all sorts of usecases ranging from verifiable computation to privacy-preserving cryptocurrency. дальше »
2018-7-21 23:03 | |
|
|
Bitcoin maximalism against narrow minded
But if Bitcoin proponents continue to ignore or attack these other applications, we may see them flourish on other networks instead. The Predestination Trap Bitcoin may very well end up the single, dominant public blockchain, but this is not guaranteed. дальше »
2018-7-3 20:01 | |
|
|
Bitmain Nears 51% of Network Hash Rate: Why This Matters and Why It Doesn’t
Recent Bitcoin block data shows that Bitcoin’s mining pools BTC. com, AntPool and ConnectBTC, respectively mined about 25. 7 percent, 16. 1 percent and 0. 2 percent of all new blocks over the past week. дальше »
2018-6-29 23:07 | |
|
|
5 Reasons Why Bitcoin Is Crashing Right Now
Despite lightning network developments, Tether’s recent audit and the Bithumb exchange responding well to a malicious attack, Bitcoin is still struggling to gain traction in today’s market. Let’s look at a few reasons why that is дальше »
2018-6-22 16:04 | |
|
|
Op Ed: Venmo Offers the Ultimate Cryptocurrency Experience
Venmo could be the ultimate cryptocurrency experience from a user-experience perspective. Any cryptocurrency that seeks to power the future of global transactions must ensure that it is supported by a payment system that is simple, user-friendly and free — like Venmo. дальше »
2018-6-11 16:51 | |
|
|