Новости о Attacks Protocol [ Фото новости ] [ Свежие новости ] | |
Hackers get away with $20 million in twin attacks on Ankr and Helio
According to an on-chain analysis by security firm BlockSec, Ankr (ANKR/USD) and stablecoin issuer Helio have lost about $20 million in a series of connected attacks. The first attack targeted a liquid staking token product offered by Ankr while the second attack targeted the Helio Protocol. дальше »
2022-12-2 13:56 | |
|
|
Super Protocol: The Solution to Web3 Crypto Hacks and Data Leaks?
Crypto hacks have become commonplace, with projects like Axie Infinity losing millions of dollars to such attacks. Hacks in 2022 alone have amounted to over $2 billion, and the year hasn’t ended yet. дальше »
2022-9-29 23:53 | |
|
|
BENQI to Integrate Chainlink Price Feeds to Secure its Protocol
BENQI, an algorithmic Liquidity Market protocol on Avalanche, has announced it will be integrating with Chainlink Price Feeds to increase security against flash loan attacks. BENQI protocol has highly reliable, and tamper-proof data feeds on all the assets offered in its lending and borrowing markets. дальше »
2021-5-19 21:02 | |
|
|
Avalanche-Based Lending Protocol BENQI Integrates Chainlink Price Feeds
Avalanche-based algorithmic money market protocol BENQI is integrating Chainlink Price Feeds to ensure protocol security against the infamous flash loan attacks. BENQI Integrates Chainlink Oracles Today, Avalanche’s C-Chain-based algorithmic money-making protocol BENQI announced it is integrating Chainlink Price Feeds to safeguard the protocol against flash loan assaults. дальше »
2021-5-19 16:09 | |
|
|
BENQI Integrates Chainlink Price Feeds on Avalanche Mainnet to Secure Lending Protocol
Coinspeaker BENQI Integrates Chainlink Price Feeds on Avalanche Mainnet to Secure Lending Protocol BENQI, an algorithmic money market protocol built on Avalanche’s C-Chain, is integrating Chainlink Price Feeds to ensure security of its protocol and resilience against flash loan attacks. дальше »
2021-5-18 15:47 | |
|
|
Bridge Mutual Launches IDO, Gives Users Control Over Risk Exposure
Attacks on major cryptocurrency exchanges are regrettably common. Over $200 million dollars have been lost to hacks and exploits on services such as KuCoin and, more recently, Origin Protocol. Although these events are an inescapable risk, there are new services that offer protection against loss of funds for these scenarios. Bridge Mutual is a decentralized […] дальше »
2021-1-30 12:39 | |
|
|
IOHK relaunches Mantis to offer Ethereum Classic community a more secure future
Global blockchain research and development company IOHK has announced that it is relaunching the ‘Mantis’ client, which was originally developed for Ethereum Classic (ETC) by IOHK in 2017. The decision to relaunch follows the recent 51% attacks on Ethereum Classic, which have exposed vulnerabilities in the protocol, making it clear that ETC is in need […] CryptoNinjas » IOHK relaunches Mantis to offer Ethereum Classic community a more secure future дальше »
2020-12-10 07:35 | |
|
|
DeFi Protocol Harvest Finance Offers $100,000 Bounty In The Aftermath Of A $24M Exploit
Several decentralized finance (DeFi) protocols have fallen victim to economic exploits since the start of this year. These have included large-scale attacks on the bZx project, the $25 million exploit on dForce’s lending protocol LendfMe. дальше »
2020-10-26 14:33 | |
|
|
Ethereum Classic Devs Propose 51% Attack Prevention Protocol
After multiple 51% attacks, Ethereum Classic (ETC) developers working towards making the project’s network more resistant to blockchain reorganization (reorg) exploits. Proof-of-Work (PoW) blockchains with significantly smaller network effect remain vulnerable to malicious reorg attacks. дальше »
2020-9-19 20:53 | |
|
|
Security report finds Monero (XMR) leads in “cryptojacking” exploits
A new cybersecurity report said privacy protocol Monero was used in most of the cryptojacking attacks traced this year. The post Security report finds Monero (XMR) leads in “cryptojacking” exploits appeared first on CryptoSlate. дальше »
2020-9-15 18:00 | |
|
|
Research: New Malware Employs Tor and Bittorrent To Steal Bitcoin and Ether
A new trojan called Krypto Cibule uses infested computers’ power to mine cryptocurrency, steal crypto wallet files, and redirect incoming digital assets to a hacker address. The malware rides on the Tor network and the Bittorrent protocol to perform attacks, according to an extensive report by cybersecurity company, ESET. дальше »
2020-9-4 12:30 | |
|
|
Ethereum Classic Ponders ‘Code Is Law’ Philosophy After Multiple 51% Attacks
After suffering two 51% attacks in a week, the ETC community is reeling. Vitalik Buterin suggested that ETC change its consensus algorithm to Proof of Stake. But is the conservative “Code Is Law” protocol ready for a change? On July 31, Ethereum Classic was hit by the first of two 51% attacks. дальше »
2020-8-7 09:38 | |
|
|
Why isn’t Ethereum Classic worth $0? Macro investor asks after 51% attacks
Ethereum Classic (ETC), the fork or version of the Ethereum protocol that didn’t freeze the funds of the infamous DAO hack, has been under the spotlight over the past week. The post Why isn’t Ethereum Classic worth $0? Macro investor asks after 51% attacks appeared first on CryptoSlate. дальше »
2020-8-7 09:00 | |
|
|
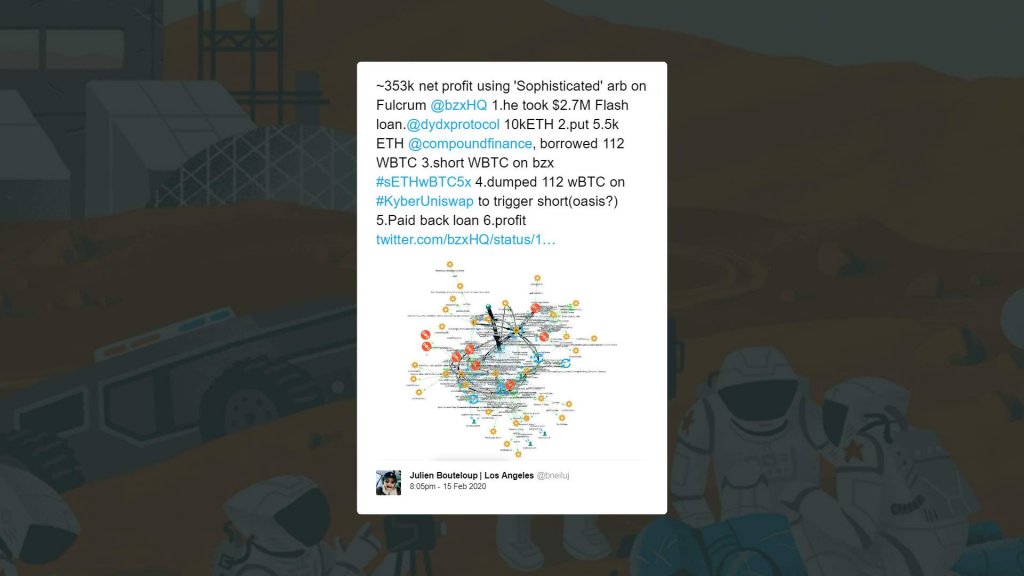
DeFi attacks reignite centralization dilemma, debates on protocol reliability
With so much innovation going on in the space, DeFi has become a big rising star over the years. In a more recent milestone, DeFi apps on the Ethereum network hit an all-time high of $1.21 billion on The post DeFi attacks reignite centralization dilemma, debates on protocol reliability appeared first on AMBCrypto. дальше »
2020-2-26 22:30 | |
|
|
DeFi lending protocol bZx exploit leads to a $1 million loss
bZx, a DeFi lending protocol, was hit with a series of exploits. The attacks resulted in the loss of 3,581 ETH worth nearly $1 million. A series of unfortunate events On Feb. 14, the bZx team was alerted about a suspicious transaction that allowed the perpetrator to net a whopping $300,000 in profits. дальше »
2020-2-19 18:07 | |
|
|
Hard Problems in Cryptocurrency: Five Years Later
Special thanks to Justin Drake and Jinglan Wang for feedback In 2014, I made a post and a presentation with a list of hard problems in math, computer science and economics that I thought were important for the cryptocurrency space (as I then called it) to be able to reach maturity. дальше »
2019-11-25 04:03 | |
|
|
BIP 324: A Message Transport Protocol That Could Protect Bitcoin Peers
BIP 324, proposed by Jonas Schnelli, is designed to protect Bitcoin peers against man-in-the-middle attacks using an action called a “handshake” to share keys more privately. The post BIP 324: A Message Transport Protocol That Could Protect Bitcoin Peers appeared first on Bitcoin Magazine. дальше »
2019-11-14 20:38 | |
|
|
Vitalik Buterin Thinks Proof of Stake Will Make Ethereum Safer than Bitcoin
Ethereum founder and programmer Vitalik Buterin thinks the Proof-of-Stake protocol will make the Ethereum blockchain safer than Bitcoin in the next few years according to a press release dated October 9, 2019, from Decrypt. дальше »
2019-10-10 13:00 | |
|
|
In-person meatspace protocol to prove unconditional possession of a private key
Recommended pre-reading: https://ethresear. ch/t/minimal-anti-collusion-infrastructure/5413 Alice slowly walks down the old, dusty stairs of the building into the basement. She thinks wistfully of the old days, when quadratic-voting in the World Collective Market was a much simpler process of linking her public key to a twitter account and opening up metamask to start firing off votes. дальше »
2019-10-2 04:03 | |
|
|
Bitcoin core developer opens draft BIP protocol Erlay for review; promises to reduce bandwidth consumption
Pieter Wuille, one of the most active Bitcoin core developers, has proposed a new BIP protocol called Erlay which would help the network grow further and secure it against numerous attacks. Bitcoin works on the principle of DLT, which is why the security of the network depends on the connectivity among these nodes. дальше »
2019-9-27 23:30 | |
|
|
The Dawn of Hybrid Layer 2 Protocols
Special thanks to the Plasma Group team for review and feedback Current approaches to layer 2 scaling - basically, Plasma and state channels - are increasingly moving from theory to practice, but at the same time it is becoming easier to see the inherent challenges in treating these techniques as a fully fledged scaling solution for Ethereum. дальше »
2019-9-2 04:03 | |
|
|
Cloudflare’s Magic Transit lets you push your entire IP traffic through its servers
Cloudflare today announced the launch of its latest network security product, called Magic Transit. This service allows organizations to send their entire network traffic through Cloudflare’s secure and performance-optimized network, offering protections against DDoS attacks, while simultaneously boosting speeds. дальше »
2019-8-13 15:59 | |
|
|
DAPI meant to resolve barriers to crypto-adoption, claims Dash Core Group’s Ryan Taylor
Ryan Taylor, CEO of Dash Core Group, was in the news last week after he claimed that the implementation of Chainlock protocol would make the network immune to 51% attacks and a chain re-org. Dash is in the news yet again, for their soon to be released Decentralized API [DAPI]. дальше »
2019-7-24 23:30 | |
|
|
Interview with Norbert Goffa: On-Chain Data Storage Solutions and New Principles of Blockchain Utilization
Just two months ago, ILCoin introduced a unique Command Chain Protocol (C2P) consensus to the crypto-community, which is resistant to quantum attacks and 51% attacks. This technology has been recognized by tech industry experts and was awarded a cybersecurity certificate by the Palo Alto Networks Partner. дальше »
2019-7-17 16:06 | |
|
|
Chainlock makes Dash immune to 51% attacks, claims Ryan Taylor
Dash was recently in the news for the implementation of Chainlock, a protocol which helps the Dash network become immune to 51% attacks or a chain re-org. Ryan Taylor, Dash CEO, was recently featured in an interview where he spoke extensively on Chainlock, New InstantSend and more. дальше »
2019-7-14 00:30 | |
|
|
Sidechains vs Plasma vs Sharding
Special thanks to Jinglan Wang for review and feedback One question that often comes up is: how exactly is sharding different from sidechains or Plasma? All three architectures seem to involve a hub-and-spoke architecture with a central “main chain” that serves as the consensus backbone of the system, and a set of “child” chains containing actual user-level transactions. дальше »
2019-6-14 04:03 | |
|
|
Ethereum’s Vitalik Buterin: IOTA’s Coordicide seems like a clone of Avalanche
IOTA Foundation, the main pillar behind the development of IOTA, recently unveiled the blueprint for Coordicide, the killer of Coordinator, which is expected to launch in the coming months. A Coordinator [Coo] is a centralized protocol that controls the transactions and security on the IOTA blockchain, with its key function being protecting Tangle against attacks. дальше »
2019-5-30 15:51 | |
|
|
Command Chain Protocol: PoW with Bulletproof Technology Under the Hood
Coinspeaker Command Chain Protocol: PoW with Bulletproof Technology Under the HoodWhile blockchain industry still strongly needs a protocol that can withstand double spending, rollbacks, and 51 percent attacks, ILCOIN project launched the first quantum resistant PoW protocol, which seeks to tap into the weaknesses of blockchain tech. дальше »
2019-4-29 09:53 | |
|
|
New Cryptojacking Campaign Infects Asia Using More Profitable Tactics
Cryptojacking — the process of infecting computers with malware to mine cryptocurrency — has declined alongside prices during cryptowinter. But like any dextrous organism facing extinction, the virus and its propagators are adapting. дальше »
2019-4-27 22:07 | |
|
|
Verifiable Delay Function (VDF) Development is Underway with Protocol Labs and ETH Foundation Project
A verifiable delay function, or a VDF, is a relatively new concept, helping to defend a system against manipulation or attacks as a result of generating somewhat random values. This type of solution can be implemented in many different use cases, including the selection of a lottery winner on the blockchain, considering that VDFs could […] дальше »
2019-4-23 01:36 | |
|
|
Op Ed: Why Bitcoin’s “Toxic” Maximalism Makes Sense
Over the years, Bitcoin has gained a reputation for having a “toxic” community of users around it. This accusation is mostly thrown at Bitcoin by proponents of altcoins and those who have supported various Bitcoin hard fork attempts in the past. дальше »
2019-4-5 16:23 | |
|
|
VeriBlock’s Bitcoin-Backed Security Protocol Goes Live
After a year on its testnet, the VeriBlock blockchain went live yesterday on the Bitcoin mainnet, allowing exchanges, wallet providers, merchants and other crypto businesses to leverage Bitcoin’s robust blockchain security. дальше »
2019-3-27 19:35 | |
|
|
Monero Upgrade Successful: Improved ASIC Resistance, Security, and Privacy
Monero successfully completed a scheduled protocol upgrade (hard fork) on Mar. 9th. The upgrade includes tweaks to the PoW algorithm for better ASIC-resistance, changes to mitigate big bang attacks, and increased transaction homogeneity to further improve privacy. дальше »
2019-3-10 00:53 | |
|
|
Mt. Fox: Fake Exchange Creator Aims to Prevent a Real Crypto Disaster
Fantasy fans may remember Arwen, the character from the “Lord of the Rings” who guides the main characters through a series of dangerous situations. The Arwen protocol intends to do the same, only for cryptocurrency trading. дальше »
2019-3-4 20:14 | |
|
|
BetterHash Protocol Lets Pool Miners Regain Control Over Their Hash Power
One problem that concerns many is the centralization of mining within the Bitcoin ecosystem. Fortunately, there are talented developers working to solve this problem and Matt Corallo, full-time Bitcoin developer at Chaincode Labs, is one of them. дальше »
2019-1-26 23:50 | |
|
|
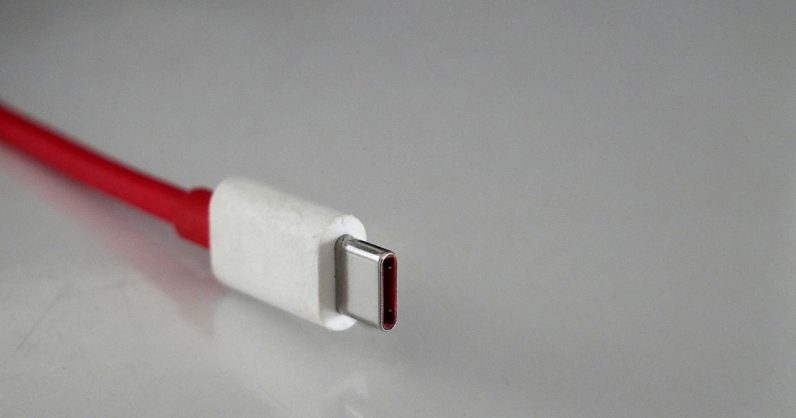
New USB-C protocol could save your devices from faulty chargers
To protect devices from damage through incompatible chargers and malware attacks, USB Implementers Forum (USB-IF) – the organization that supports and promotes changes for USB standards – has introduced an authentication program for USB-C connections. дальше »
2019-1-3 10:16 | |
|
|
Blockchain Analysis Is About to Get Harder as P2EP Enters Testing Phase
Yet another tool is being added to Bitcoin’s growing number of privacy solutions. Thought up at a brainstorming event attended by Bitcoin developers and privacy researchers last summer, Pay to Endpoint (P2EP) is a relatively new trick that utilizes the well-known CoinJoin mixing technique to make blockchain analysis much harder. дальше »
2019-1-1 19:31 | |
|
|
Syncing Data Between Bitcoin Nodes Is About to Get Easier
Minisketch is a new solution that’s trying to solve an old problem. Spearheaded by Blockstream co-founder Pieter Wuille, Bitcoin Core contributor and fellow Blockstream co-founder Gregory Maxwell, and Blockstream software engineer Gleb Naumenko, the open-source initiative is designed to achieve set reconciliation between the mempools of each full node. дальше »
2018-12-18 18:48 | |
|
|
DASH Cryptocurrency Payment Network to Apply ‘ChainLocks’ to Eliminate 51% Blockchain Attacks
The Dash, which is a payment network will soon be introducing a unique new network upgrade, one that will be able to eliminate the threat of having about 51% attacks that happen on the protocol. With the ChainLocks platform, it is able to enable the transactions to be easily secured and confirmed once the block […] дальше »
2018-12-3 22:03 | |
|
|
ChainLocks: Dash Upgrade To Eliminate 51 Percent Attacks
Payments network Dash (DASH) may soon implement a new, unique network upgrade that will reportedly “eliminate” the threat of a 51% attack from the protocol, once fully implemented ChainLocks enables transactions to be confirmed and secured as soon as the block has been processed, rather than waiting for six other blocks to be signed first. дальше »
2018-12-3 00:06 | |
|
|
Zero-Confirmation Forfeits: Adding Security to Unconfirmed BCH Transactions
On Nov. 20, the Bitcoin Cash developer Awemany announced the first code proposal for a concept called Zero-Confirmation Forfeits (ZCF), a protocol that adds a layer of security to zero-confirmation transactions. дальше »
2018-11-22 22:50 | |
|
|
Hoskinson: Satoshi Did “An Amazing Thing”...But There Are Lessons to Learn
Charles Hoskinson is best known today as a co-founder of both Ethereum and IOHK, where he leads the research, design and development of Cardano. But before these projects, there was Bitcoin. дальше »
2018-11-20 23:08 | |
|
|
One Day After the Bitcoin Cash Hard Fork: Takeaways and Latest Developments
Bitcoin Cash, the “big block” project that forked away from the Bitcoin blockchain in August 2017, “hard forked” (split) into two different coins: “Bitcoin Cash ABC” (BCH ABC) and “Bitcoin Cash SV” (BCH SV). дальше »
2018-11-17 02:13 | |
|
|
How Monero Are Improving Human Rights With XMR
Listen Here – https://soundcloud. com/cryptodaily/how-monero-are-improving-human-rights-with-xmr Monero is considered to be the privacy coin, the currency of choice for absolute privacy. Now, privacy doesn’t necessarily mean security and we should remember that 2018 has seen a tonne of ‘Monero mining’ hacks, calling into question some of the projects integrity. дальше »
2018-10-12 17:00 | |
|
|
Ammeris ICO
Ammeris is creating a platform that is designed to host frictionless interconnectivity. The Platform is now onboarding and incubating businesses and organizations seeking to use a sustainable and long-term oriented network for their applications that is easy and cost efficient to use –creating the beginning steps of a global decentralized ecosystem. дальше »
2018-9-6 05:33 | |
|
|
Algorand ICO
Algorand is a new cryptocurrency that confirms transactions with latency on the order of a minute while scaling to many users. Algorand ensures that users never have divergent views of confirmed transactions, even if some of the users are malicious and the network is temporarily partitioned. дальше »
2018-8-7 02:57 | |
|
|