Code - Свежие новости [ Фото в новостях ] | |
Hyperledger Blockchain Project Adds 9 New Members, Passes 250 Total In Community
Hyperledger has recently announced that it has surpassed the 250 member mark with the addition of nine new members. Hyperledger is an open source collaborative effort created to advance cross-industry blockchain technologies. дальше »
2018-8-1 09:30 | |
|
|
Digital Asset Research (DAR) Claims TRON has Plagiarized Code, Justin Sun Responds
Has Justin Sun of Tron Committed Plagiarism? Here’s His Answer… Virtual research specialists at DAR discovered something shady happening inside Tron’s source code. Developers at the company found some unfortunately distinguishable lines of code inside the platform that were also found in other cryptocurrency codes. Plagiarism is looked down upon in crypto as much as […] дальше »
2018-7-31 22:10 | |
|
|
Women, tech and finance coverage, what does the future hold?
Forough is the founder of Code to Inspire, a nonprofit coding school for girls in Herat, Afghanistan that helps young women improve their technical literacy. We asked her to share her thoughts on how technology—and crypto specifically—is empowering young women in her home country. дальше »
2018-7-31 22:00 | |
|
|
Steam removes controversial game accused of mining cryptocurrency
Steam has removed “trivial platformer” game Abstractism from its store following accusations that the game is surreptitiously stealing users’ computing power to mine cryptocurrency. “We have removed Abstractism and banned its developer from Steam for shipping unauthorized code, trolling with content, and scamming customers with deceptive in-game items,” Doug Lombardi, VP of Marketing at Steam, told Hard Fork in an email. дальше »
2018-7-31 12:50 | |
|
|
Cryptocurrency Wallet SafeWallet Introduces Alternative to Private Keys and Mnemonic Phrases
In a bid to entirely eradicate the issues of loss, theft and other challenges that comes with crypto wallet private keys and mnemonic phrases, SafeWallet has introduced a new system of wallet security that enables users recover their digital currencies with just their QR code based user IDs and preset security questions, according to a press release by the firm. дальше »
2018-7-30 17:00 | |
|
|
Hackers Attack Compromises Ethereum Block Explorer Site Etherscan.io
On July 23, 2018, the most popular Ethereum block explorer site Etherescan. io was hit malicious attack. According to Motherboard, the hackers were able to use the website’s comments section to introduce malicious code. дальше »
2018-7-29 03:00 | |
|
|
QR Code Encrypted Private Keys to be Replaced by Crypto Wallet
Decentralized cryptocurrency wallet SafeWallet is launching a new QR code-based user identification system to replace mnemonic phrases and private keys, the firm announced Friday. The app, operated by China-based Cheetah Mobile, will use a two-tier security system to grant users access to their holdings, according to a press release. The first stage will have users scan дальше »
2018-7-27 20:25 | |
|
|
Who controls the Bitcoin Core? And it’s not Wladimir J. van der Laan
So a recent thread on Reddit raised the question of who is actually in control of Bitcoin Core; the code repository of the world’s first and largest cryptocurrency; Bitcoin. The Bitcoin Core code repository is the direct descendant of the original code that was made and released to the world by Satoshi Nakamoto. дальше »
2018-7-27 13:30 | |
|
|
What Is Ethereum Classic (ETC)? A Smart Contract Platform Betting on the ‘Code Is Law’ Philosophy
The main difference between Ethereum Classic (ETC) and Ethereum (ETH) is on ideological level - ETH vision is that blockchain records should be revised if the majority of the community decides so, while the ETC belief is that code is law and дальше »
2018-7-27 11:50 | |
|
|
Marqyt ICO
Main objective of Marqyt is to reduce the number of counterfeit goods, thereby increasing the profitability of original productions and clearing the market of low-quality counterfeit products. Using the application MARQYT, the producer or the manufacturer will be able to enter certain information about its product in the blockchain in a few clicks. дальше »
2018-7-26 17:02 | |
|
|
Etherscan Block-Explorer Hit by ‘Harmless’ Hack
Visitors to the Etherscan. io website were panicking on Monday when faced with a pop-up indicating that the site had been hacked. The popular Ethereum blockchain-explorer quickly fixed the breach and no data was compromised — this time. дальше »
2018-7-26 22:00 | |
|
|
Welcome To Crypto Park: Review Of Proxeus Beta
One of the most worrying trends in cryptocurrency is the tendency to over-rely on code and programming to prevent accidents. It’s the “Jurassic Park” problem—clever engineers can prepare for every problem they can imagine, but not the ones they can’t. дальше »
2018-7-25 17:44 | |
|
|
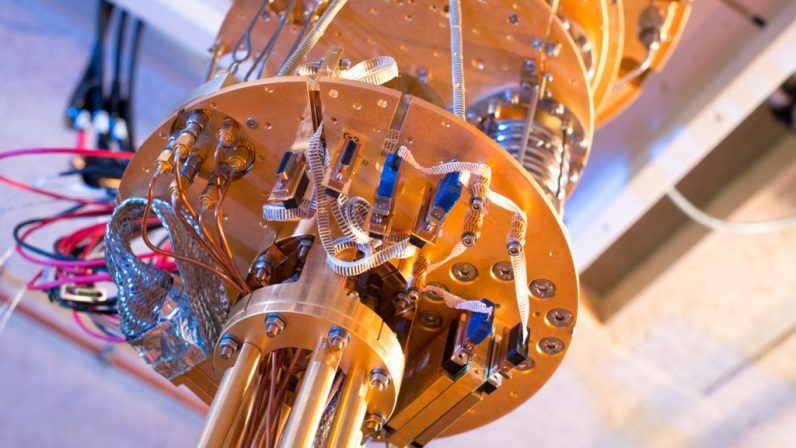
Microsoft debuts free quantum computer programming katas
Microsoft yesterday announced the release of Quantum Katas, a self-paced programming project that teaches developers how to write code for quantum computers. Quantum Katas, as the name implies, are coding katas from Microsoft that teach beginning developers the fundamentals of the company’s quantum computer programming language called Q#. дальше »
2018-7-24 19:57 | |
|
|
Google Cloud partners with DLT-startup Digital Asset for blockchain-based tools
DLT-solutions provider Digital Asset announced about partnership with Google Cloud in order to create a platform for deploying blockchain-based solutions without having to write the code from ground zero. дальше »
2018-7-24 14:53 | |
|
|
Etherscan rushes to plug vulnerabilities following strange hacking attempts overnight
Etherscan, the most widely used Ethereum blockchain explorer, has quickly patched security vulnerabilities overnight as hackers exploited certain parts of its service. Hackers successfully manipulated the Disqus API – a third-party service used by Etherscan that allows for comments to be left on Ethereum wallet addresses. дальше »
2018-7-24 13:00 | |
|
|
Trade.io Launches Community-Led Exchange With Peer Liquidity Pool
Trade. io, a new exchange, has launched and is serving its first 1000 users, with more on a waiting list. The exchange is currently offering crypto trading only, but has plans to branch out into “asset classes such as forex, commodities and others. дальше »
2018-7-24 06:35 | |
|
|
Google Cloud Joins Digital Asset to Assist Solutions Architects Code Blockchain Applications
The collaboration of the Internet giant and a company with a strong expertise in distributed ledger technology is expected to become beneficial for both parties. Google Cloud will get an opportunity to increase its market share while fintech company can reach new audiences. дальше »
2018-7-24 22:53 | |
|
|
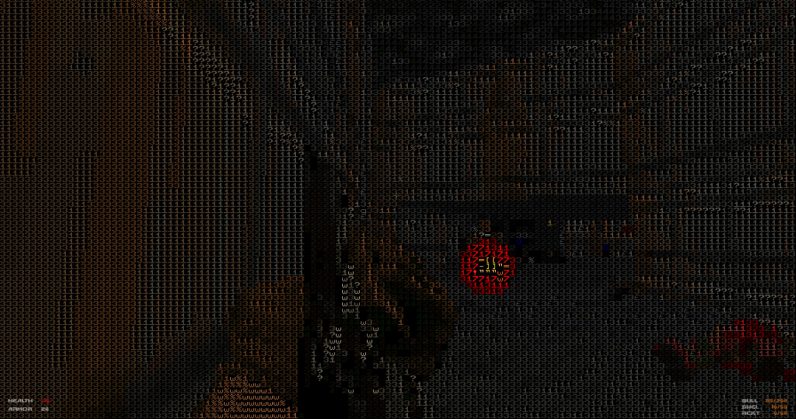
DOOM in ASCII mode is equal parts fun and frustrating
You don’t really need an excuse to revisit id Software’s genre-defining FPS game, DOOM – but indie developer Dario Zubovoic’s take on the classic is good enough reason to jump back into the gory shooter for a few rounds. дальше »
2018-7-23 09:46 | |
|
|
Governance, Part 2: Plutocracy Is Still Bad
Coin holder voting, both for governance of technical features, and for more extensive use cases like deciding who runs validator nodes and who receives money from development bounty funds, is unfortunately continuing to be popular, and so it seems worthwhile for me to write another post explaining why I (and Vlad Zamfir and others) do not consider it wise for Ethereum (or really, any base-layer blockchain) to start adopting these kinds of mechanisms in a tightly coupled form in any significant way. дальше »
2018-7-21 23:03 | |
|
|
A Prehistory of the Ethereum Protocol
Although the ideas behind the current Ethereum protocol have largely been stable for two years, Ethereum did not emerge all at once, in its current conception and fully formed. Before the blockchain has launched, the protocol went through a number of significant evolutions and design decisions. дальше »
2018-7-21 23:03 | |
|
|
STARKs, Part I: Proofs with Polynomials
Special thanks to Eli Ben-Sasson for ongoing help, explanations and review, coming up with some of the examples used in this post, and most crucially of all inventing a lot of this stuff; thanks to Hsiao-wei Wang for reviewing Hopefully many people by now have heard of ZK-SNARKs, the general-purpose succinct zero knowledge proof technology that can be used for all sorts of usecases ranging from verifiable computation to privacy-preserving cryptocurrency. дальше »
2018-7-21 23:03 | |
|
|
Notes on Blockchain Governance
In which I argue that “tightly coupled” on-chain voting is overrated, the status quo of “informal governance” as practiced by Bitcoin, Bitcoin Cash, Ethereum, Zcash and similar systems is much less bad than commonly thought, that people who think that the purpose of blockchains is to completely expunge soft mushy human intuitions and feelings in favor of completely algorithmic governance (emphasis on “completely”) are absolutely crazy, and loosely coupled voting as done by Carbonvotes and similar systems is underrated, as well as describe what framework should be used when thinking about blockchain governance in the first place. дальше »
2018-7-21 23:03 | |
|
|
Buterin: Ethereum Can’t be Forced to Adopt Code I Write, Merit of Decentralization
At the TechCrunch: Sessions Blockchain 2018 hosted in Zug, Switzerland, Ethereum Creator Vitalik Buterin explained the decentralized nature of the Ethereum blockchain and the merit of eliminating single points of failure. дальше »
2018-7-21 21:00 | |
|
|
Here’s how to pass 12 CompTIA certification exams — for less than $3 each
You can round out your skill set with a “greatest hits” package of their top-notch training with the Complete 2018 CompTIA Certification Training Bundle. It’s only $29.50 (an over 90 percent savings) from TNW Deals with coupon code: DIGITALWEEK50. дальше »
2018-7-21 17:00 | |
|
|
Penn Study: 4 In 5 Leading ICOs Don’t Keep Promises and May Contain Backdoors
According to new research findings from the University of Pennsylvania, many ICOs are taking their investors’ trust for granted. Not only do ICO developers seem to not implement promised features, the investment market as a whole seems to be optimal for ICOs that can be modified at any time. The researchers dug deep into code […] дальше »
2018-7-21 06:25 | |
|
|
UK Law Commission To Start Research Into ‘Smart Contracts’
The legal research body’s recent report includes plans to study executable distributed code contracts.
дальше »2018-7-21 21:36 | |
|
|
Last Test Network Launched for the Ethereum Payments Channel Raiden
A new test network has been announced for Raiden, the ethereum payments channel project during the Dappcon developer conference in Berlin on Thursday, July 19. This particular testnet is the last one to test the technology before going live for everyday users. дальше »
2018-7-20 19:27 | |
|
|
Final Test Network Launched for Ethereum Payments Channel Raiden
The final testnet features a preventative recovery mode implemented through a rewritten smart contract code. The post Final Test Network Launched for Ethereum Payments Channel Raiden appeared first on CoinSpeaker. дальше »
2018-7-20 16:55 | |
|
|
ARK Revamps Software Development Kits To Streamline Implementation
A new platform designed to bridge blockchains with special lines of communication called SmartBridges has been released to revamp SDKs. The new announcement states ARK has redeveloped much of the code for the new project’s 15 SDK from nothing, to speed up the rate at which it can be implemented and maintained from the codebase. […] дальше »
2018-7-20 12:57 | |
|
|
Penn Study: 4 In 5 Leading ICOs Don’t Keep Promises and May Contain Backdoors
According to new research findings from the University of Pennsylvania, many ICOs are taking their investors’ trust for granted. Not only do ICO developers seem to not implement promised features, the investment market as a whole seems to be optimal for ICOs that can be modified at any time. дальше »
2018-7-20 03:49 | |
|
|
Many ICOs The protocols are gradually showing
The study finds that there are glaring differences between what the ICOs’ code delivers and what the creators promised to their investors. Only 20% of 50 ICO Codebases Matched the Promoter’s Promises Out of the 50 ICOs surveyed, using both the white papers (contracts) and the codebases (delivered or non-delivered promises), a great deal of дальше »
2018-7-20 00:56 | |
|
|
New Research Finds Backdoor ‘Centralized Control’ in Many ICOs
Researchers from the University of Pennsylvania have found that a significant number of ICOs retained centralized control through undisclosed code. Backdoor Centralization The full paper, titled Coin-Operated Capitalism and published on July 18, is an “interdisciplinary effort spanning law, economics, and computer science,” according to University of Pennsylvania Law Professor David Hoffman. дальше »
2018-7-20 23:00 | |
|
|
Study Shows Many ICO Protocols Fail to Match White Paper Promises
On July 19, a group of interdisciplinary researchers from the University of Pennsylvania, with guidance from the esteemed Penn Law professor David Hoffman, published an in-depth study of initial coin offerings (ICOs) that promise innovative concepts like autonomous governance and operate by the belief that ‘code is law’. дальше »
2018-7-19 22:04 | |
|
|
Far From Finished: Ethereum’s Hottest Bone to Pick
A relatively minor suggestion, Schoedon asked to advance EIP 999 within the parameters of ethereum’s process for code review. But the move had wider repercussions, with sometimes vitriolic debate surfacing on Twitter, Github and Reddit. дальше »
2018-7-19 19:00 | |
|
|
Russian Lawmakers are Looking to Pass the Bill on Cryptocurrencies
The document will not include separate taxation schemes for cryptocurrency owners, which means that mining and circulation of cryptocurrencies will be regulated under existing provisions of the Russian Tax Code. дальше »
2018-7-19 12:29 | |
|
|
Russia: Crypto Miners and Holders Regulated
Cryptocurrency miners and holders in Russia will be regulated under the Internal Revenue Code, local news outlet Izvestiya reported July 18. The Chairman of the Russian State Duma Committee on Financial Markets, Anatoly Aksakov, told Izvestiya that lawmakers are looking to pass the bill on digital financial assets, or cryptocurrencies, during the autumn session of дальше »
2018-7-19 07:34 | |
|
|
Malware Mining Now More Dangerous than Ransomware, according to Report
Illicit cryptocurrency mining, or “cryptojacking,” has become more popular among cybercriminals than ransomware, according to a report by Skybox Security. In its mid-year update, the firm said that crypto miners now account for 32 percent of all cyberattacks, while ransomware only makes up 8 percent. дальше »
2018-7-19 23:11 | |
|
|
Blockchain Startup Launches Platform for Risk-Managed ICO Investments
CoinMirror, a Berlin-based startup, is launching the public beta of its platform for ICO investments on the Ethereum mainnet today, July 18, 2018. The platform seeks to provide investment opportunities to investors regardless of available capital. дальше »
2018-7-18 18:41 | |
|
|
Review of top 50 ICOs shows most promise things they will never deliver
The most extensive legal report on initial coin offerings (ICOs) is now available to the general public, and the findings are pretty damning. University of Pennsylvania legal professors, alongside research teams, have meticulously studied the top 50 highest grossing ICOs of last year – their whitepapers and their code – to determine if there was any disparity between promises made and cryptocurrencies developed. дальше »
2018-7-18 17:30 | |
|
|
There is the threat of cryptoming malware
For example, recent research from Imperva shows that 75 percent of Redis servers are infected with cryptomining malware. To carry out cryptomining attacks, hackers will first look for an RCE vulnerability, which allows attackers to run arbitrary code on the vulnerable server. дальше »
2018-7-18 02:42 | |
|
|
A beginner’s guide to AI: Computer vision and image recognition
This is the second story in our continuing series covering the basics of artificial intelligence. While it isn’t necessary to read the first article, which covers neural networks, doing so may add to your understanding of the topics covered in this one. дальше »
2018-7-18 02:15 | |
|
|
Op Ed: Addressing the Threat of Cryptomining Malware
One major class of attacks to hit the hacking landscape recently is cryptomining. While cryptomining on its own supports a good cause when being done consciously, it also allows nefarious actors to make a lot of money fast, and, with the sheer number of cryptocurrencies available to mine, it is becoming a popular choice for attackers. дальше »
2018-7-18 23:18 | |
|
|
The ongoing Hacks Highlight is essential for better protection, reformed transactions, says DEX.top
“Well constructed” contract code is the key, and all exchanges must focus on this in order to gain and keep users’ trust. The Sad Story of Exchange Hacks Continues Catastrophic hacks resulted in millions of dollars lost at early bitcoin exchanges like Mt. дальше »
2018-7-18 22:44 | |
|
|
JavaScript runs the Web — so learn to run JavaScript with training under $15
JavaScript is one of the most versatile tools a web developer can swing — and you can get the complete JS exposure with the training found in the Essential JavaScript Coding Bundle. It’s available right now from TNW Deals for only $15, an over 90 percent savings with coupon code "DIGITALWEEK50." дальше »
2018-7-17 17:00 | |
|
|
League of Legends PH Client Facilitated Cryptojacking Due to Modified Code
Popular online games have always been a prone target for criminals and hackers. Although these incidents are usually aimed at collecting users’ in-game items or payment information, a new trend has begun to emerge. дальше »
2018-7-16 20:00 | |
|
|